Akira ransomware gang: Who they are and how to prevent infection
Who is the Akira ransomware gang and how can you block them?
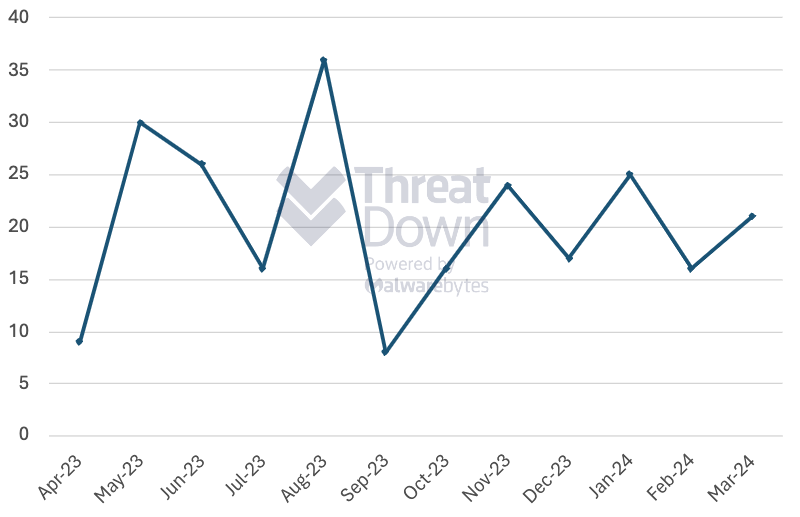
Since we first observed them in April 2023, the Akira ransomware gang has made a big name for itself in a short time. With 244 confirmed attacks from April 2023 to March 2024, Akira has already become the eighth most prolific ransomware gang since we began tracking all gangs in February 2022.
Akira made headlines in April after the Cybersecurity and Infrastructure Security Agency (CISA) FBI announced that the gang made $42 million from 250 attacks since March 2023, or an average of $3,500,000 a month. The CISA report also details Akiras’ Tools, Tactics, and Procedures (TTPs).
While the CISA advisory on Akira is a must-read for organizations looking for in-depth technical information on Akira’s ransomware, this post will be more focused on Akira’s victimology and prevention strategies. Let’s dive into it.
Akira ransomware gang victimology
Akira’s victimology doesn’t differ much from a majority of ransomware gangs, with an outsized focus on the US and the Services industry. That said, there is at least one industry they attack at an above-average rate: Education. At 19 total attacks, Akira attacks educational organizations at roughly twice as much as average for all gangs (9 attacks).
Akira mainly attacks the US organizations (149 attacks), which is in line with overall trends, though they attack Australian organizations at slightly an above-average rate (7 attacks).
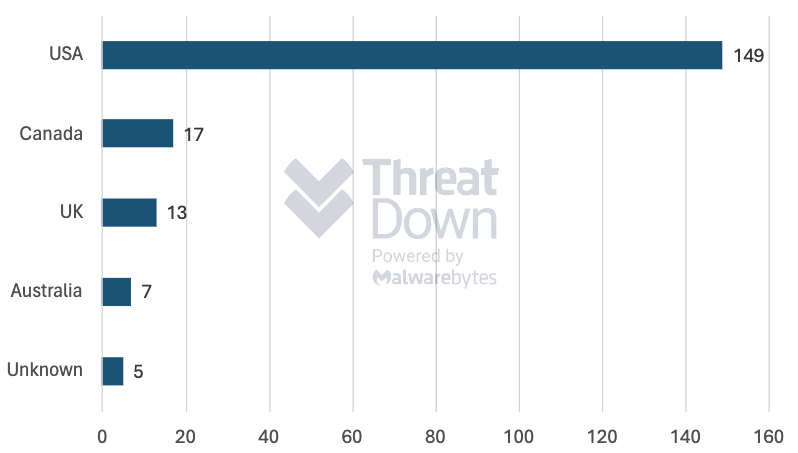
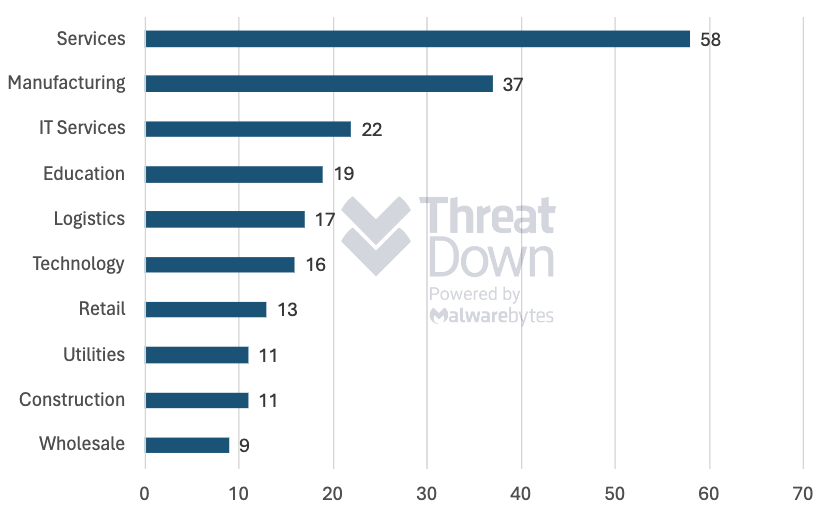
The main takeaway from Akira’s victimology: while Akira doesn’t seem to disproportionally attack any one sector or country, educational organization and and Australian organizations should be slightly more alert to potential targeted attacks by this gang.
Akira ransomware gang ransom note
Filename: akira_readme.txt
Hi friends,
Whatever who you are and what your title is if you’re reading this it means the internal infrastructure of your company is fully or partially dead, all your backups – virtual, physical – everything that we managed to reach – are completely removed. Moreover, we have taken a great amount of your corporate data prior to encryption.
Well, for now let’s keep all the tears and resentment to ourselves and try to build a constructive dialogue. We’re fully aware of what damage we caused by locking your internal sources. At the moment, you have to know:
- Dealing with us you will save A LOT due to we are not interested in ruining your financially. We will study in depth your finance, bank & income statements, your savings, investments etc. and present our reasonable demand to you. If you have an active cyber insurance, let us know and we will guide you how to properly use it. Also, dragging out the negotiation process will lead to failing of a deal.
- Paying us you save your TIME, MONEY, EFFORTS and be back on track within 24 hours approximately. Our decryptor works properly on any files or systems, so you will be able to check it by requesting a test decryption service from the beginning of our conversation. If you decide to recover on your own, keep in mind that you can permanently lose access to some files or accidently corrupt them – in this case we won’t be able to help.
- The security report or the exclusive first-hand information that you will receive upon reaching an agreement is of a great value, since NO full audit of your network will show you the vulnerabilities that we’ve managed to detect and used in order to get into, identify backup solutions and upload your data.
- As for your data, if we fail to agree, we will try to sell personal information/trade secrets/databases/source codes – generally speaking, everything that has a value on the darkmarket – to multiple threat actors at ones. Then all of this will be published in our blog – https://akiral2iz6a7qgd3ayp3l6yub7xx2uep76idk3u2kollpj5z3z636bad.onion.
- We’re more than negotiable and will definitely find the way to settle this quickly and reach an agreement which will satisfy both of us.
If you’re indeed interested in our assistance and the services we provide you can reach out to us following simple instructions:
- Install TOR Browser to get access to our chat room – https://www.torproject.org/download/.
- Paste this link – https://akiralkzxzq2dsrzsrvbr2xgbbu2wgsmxryd4csgfameg52n7efvr2id.onion.
- Use this code – [snip] – to log into our chat.
Keep in mind that the faster you will get in touch, the less damage we cause.
How to prevent an Akira ransomware gang infection
Akira is known to gain initial access through exploiting Cisco vulnerabilities such as CVE-2020-3259 and CVE-2023-20269, making timely vulnerability assessment and patch management a must-have for organizations looking to prevent an Akira ransomware infection.
In addition to patching, we recommend disabling or hardening remote access to Remote Desktop Protocol (RDP) and VPNs, both of which Akira is known to use for initial access. We also recommend organizations across all sectors follow a few best practices to prevent (and recover) from ransomware attacks from every angle. That includes:
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
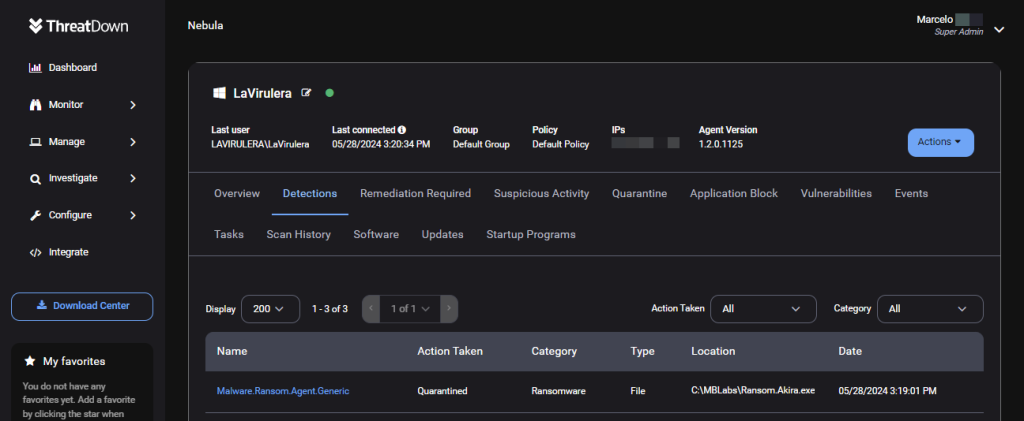
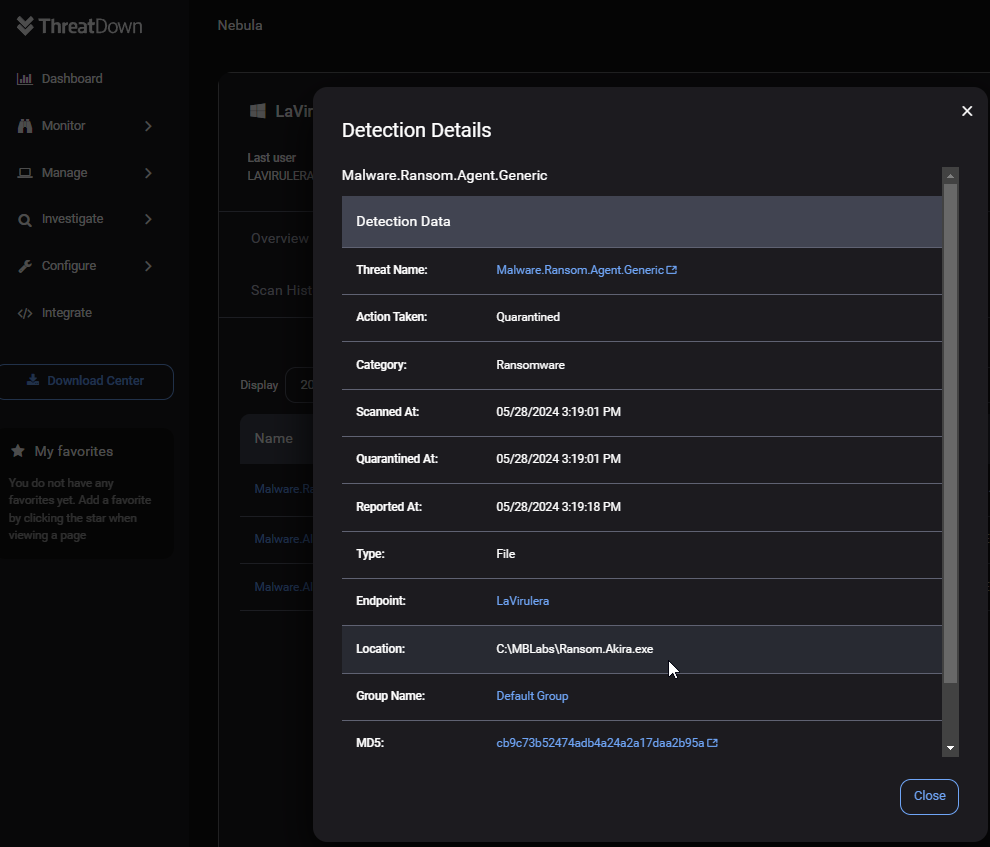
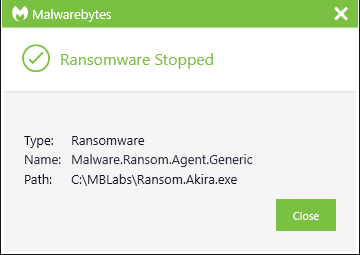
ThreatDowns’ EDR anti-ransomware layer constantly monitors endpoint systems and automatically kills processes associated with ransomware activity, including Akira ransomware.
Purpose-built for organizations with small (to non-existent) security teams that lack the resources to address threats like Akira ransomware, the ThreatDown Ultimate Bundle includes award-winning technologies and 24x7x365 expert-managed monitoring and response from the ThreatDown MDR team.