Ransomware in December 2024—Cl0p returns
December 2024 saw the unwelcome return of the notorious Cl0p ransomware gang.
December saw two significant disclosures about ransomware attacks. On December 20, 2024, US hospital operator Ascension reported that nearly 5.6 million individuals were affected by a ransomware attack in May that compromised medical records, lab tests, and insurance information. The revelation came just five days after Rhode Island disclosed a substantial data breach, with criminals demanding a ransom to prevent the release of personal information belonging to hundreds of thousands of residents, many of whom were on state assistance programs.
In better news, the US Department of Justice charged Russian-Israeli dual citizen Rostislav Panev for his alleged involvement with the LockBit ransomware group. Although it is now a shadow of its former self, LockBit was once the most feared ransomware group in the world. That changed in February 2024, when an extraordinary law enforcement action saw the LockBit website taken over and used to troll the group.
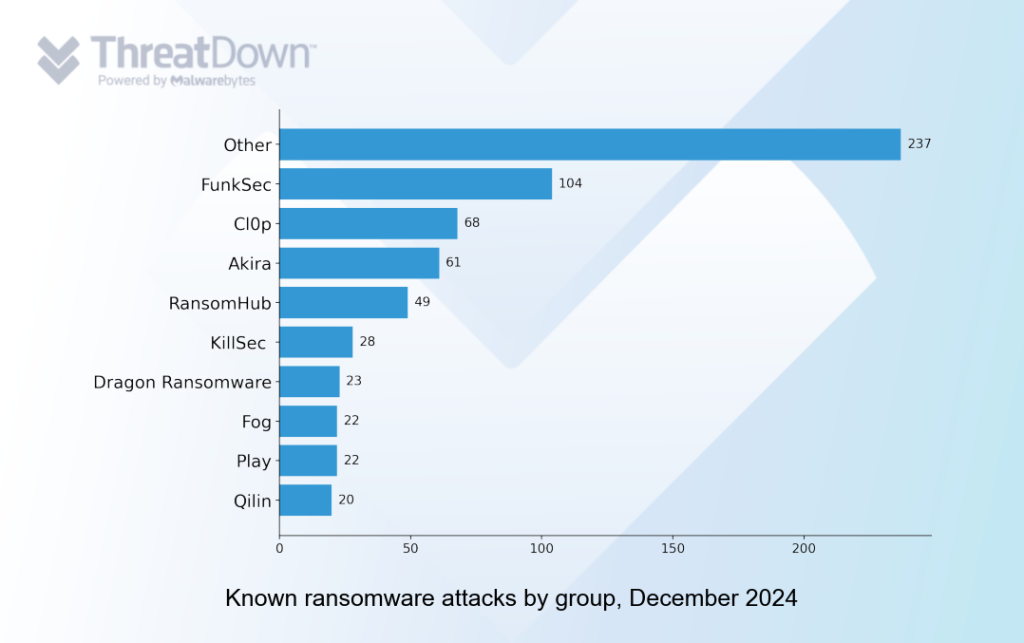
Although FunkSec was the most active group in December, recording 104 known attacks, the return of Cl0p was the most notable feature of the month’s top ten ransomware groups. Cl0p has been all but dormant since a devastating zero-day campaign against Progress MOVEit Transfer in mid-2023.
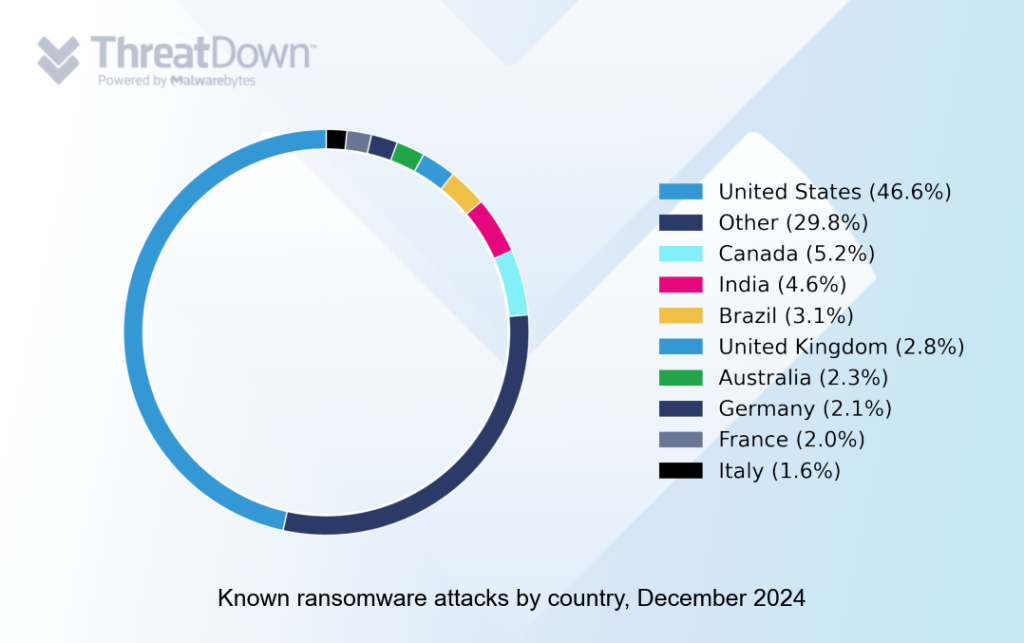
The USA was the most attacked country in December 2024, followed by Canada, India, Brazil and the UK.
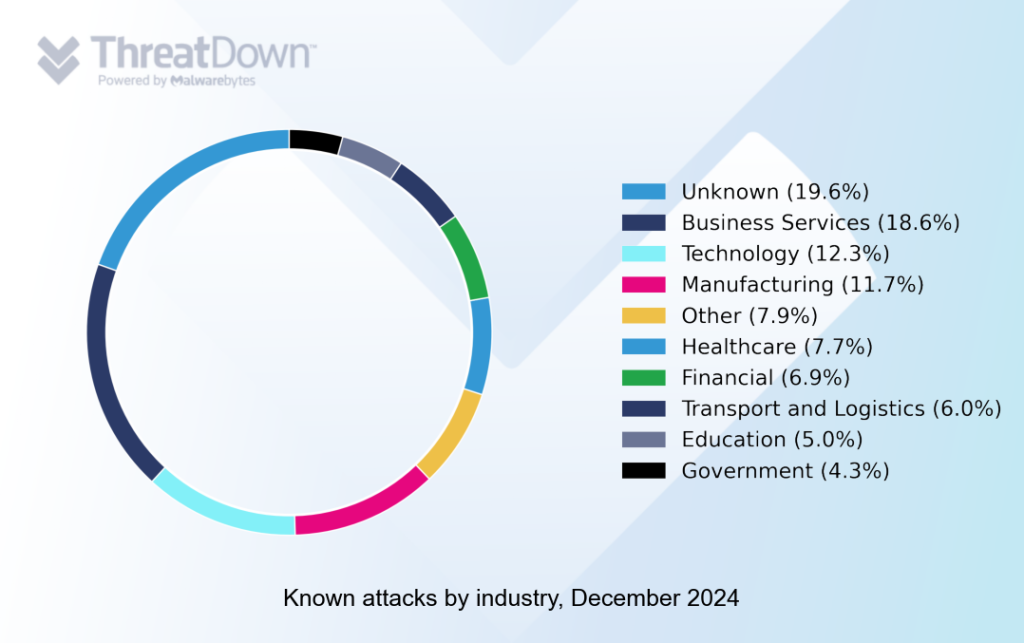
The business services sector weathered the most attacks in December 2024, followed by technology and manufacturing.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.




