Ransomware in France, April 2022–March 2023
This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their dark web sites. In this report, “known attacks” are attacks where the victim opted not to pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
Between April 2022 and March 2023, France was one of the most attacked countries by ransomware gangs. During that period:
- France was the fifth most attacked country in the world.
- The government sector was attacked more often than in similar countries.
- LockBit dominated the last twelve months, being used in 57% of known attacks.
- There were almost twice as many LockBit attacks in France than either the UK or Germany.
In July 2022, La Poste Mobile, a mobile carrier owned by French postal company La Poste, suffered a LockBit ransomware attack, severely impacting its administrative and management services. After successfully reducing the ransom demand from $1.4 million to $300,000 in a five day negotiation, La Poste Mobile’s negotiator announced on July 11, “Management doesn’t want to pay anymore … it has reconsidered its decision.” LockBit published the data it had stolen on its leak site, describing it as “the private information of more than a million and a half people in France.”

In August 2022, attackers demanded $10 million after a ruthless assault on the Center Hospitalier Sud Francilien (CHSF), a 1000-bed hospital near Paris. The disruption to CHSF’s computer systems resulted in patients having to be sent elsewhere, and surgeries having to be postponed.
A few months later, in mid-November, French defense and technology group Thales confirmed a data breach affecting contracts and partnerships in Malaysia and Italy. As with so many attacks in France in the last twelve months, the perpetrators used LockBit ransomware.
France is a prime target
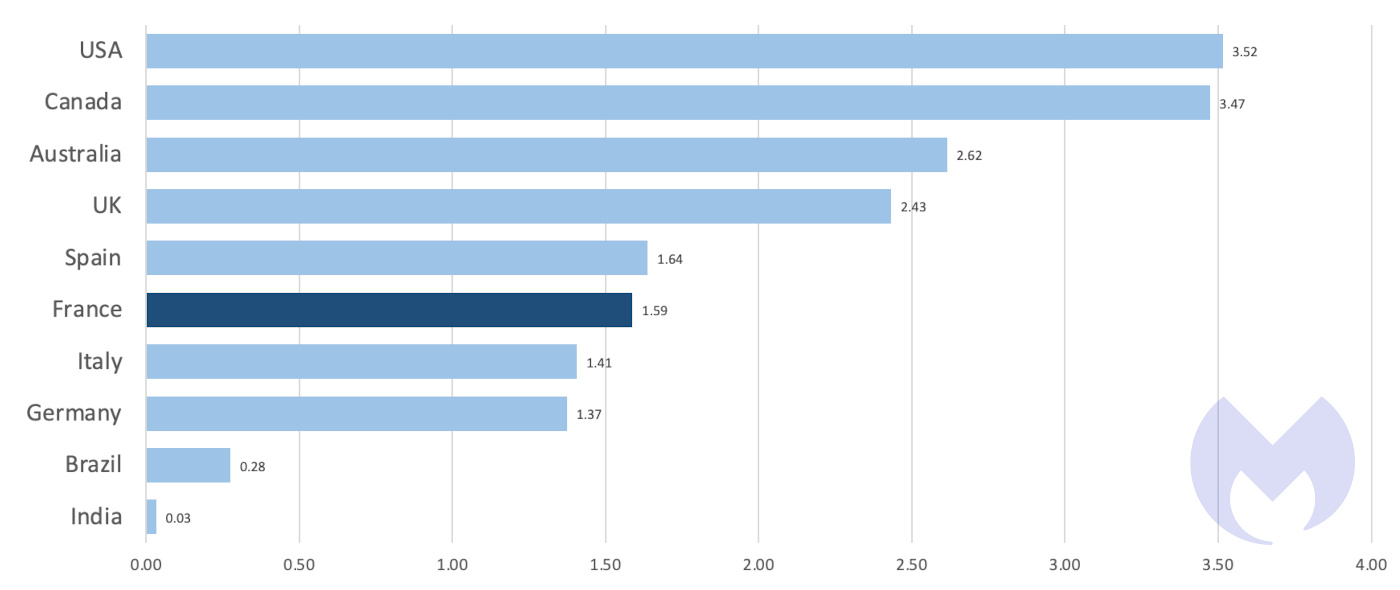
In the 12 months from April 2022 to March 2023, France was a globally significant target for ransomware, and the fifth most attacked country by known attacks.

Given the disparity between the USA and the rest of the world in terms of number of attacks it would be easy to conclude that ransomware is, first-and-foremost, a USA problem. It is not. The size and nature of the US economy means that it has many more targets for ransomware gangs than the other countries in the top ten.
We can account for the difference in the size of countries’ economies by dividing the number of known ransomware attacks by a country’s nominal GDP, which gives us an approximate rate of attacks per $1T of economic output. On that basis, the difference between France and the USA is far smaller than the total number of known attacks would suggest. And while France and Germany suffered nearly identical numbers of known attacks, France appears to suffer a much higher rate of attacks per unit of economic activity than its neighbour.

The size of the countries in the top ten also vary enormously, and we can try to account for that by dividing known attacks by the size of each country’s population. On that measure, again, the differences between countries are far smaller than a simple count of known attacks suggests.
In all the variations of our top ten, English-speaking countries occupy at least three of the top five positions, which suggests that ransomware gangs have a slight bias for English-speaking targets. France sits just below the Anglosphere in a cluster of four advanced European economies suffering nearly identical rates of attacks per capita.
By any measure, France is one of the most attacked countries in the world, and its organisations are prime targets for ransomware gangs. Unusually, government targets accounted for a significant proportion of those organisations in the last twelve months. It was the country’s third most attacked sector, accounting for 9% of known attacks. By comparison, over the same twelve month period, 4% of known attacks in the USA and 3% of known attacks in Germany affected their government sectors, while just 20 miles across the English channel, the UK experienced none at all.
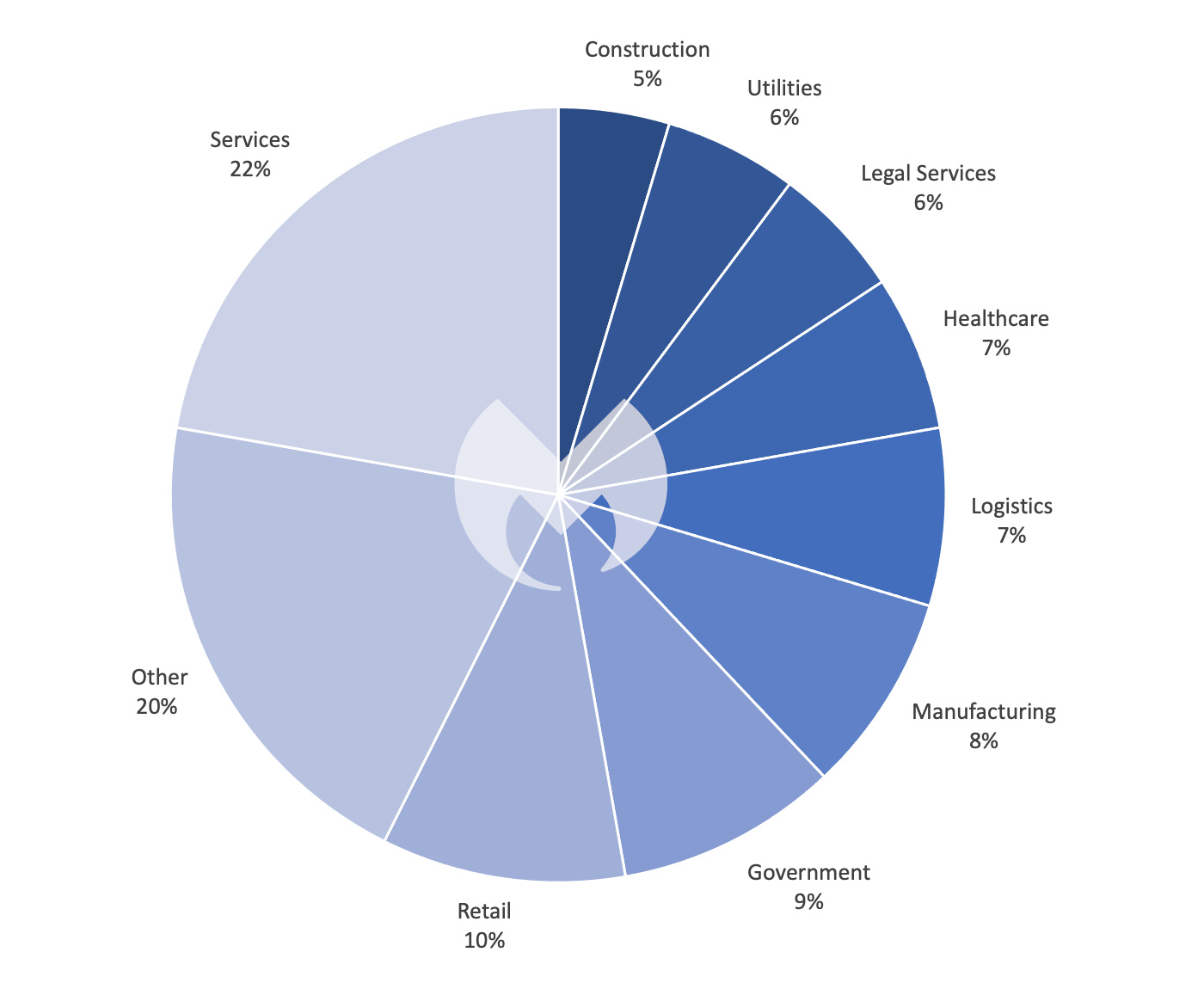
As is often the case, the reasons for this are not obvious. It is possible that this simply reflects the larger footprint of government in France—government spending accounts for a larger proportion of the economy in France than in either the UK or Germany. However, the difference is only a few percentage points.
Ransomware gangs often operate from the safe havens of Russia and the Commonwealth of Independent states, which can make it tempting to ascribe nationalistic or geopolitical motivations to their activity. However, the truth is they are businesses that choose targets that are easy to infiltrate and likely to pay substantial ransoms.
Unfortunately, the most likely explanation for the high proportion of government sector targets among the known attacks in France is that government institutions were easier targets in France than elsewhere.
LockBit’s hunting ground
The most dangerous ransomware in the world right now, is LockBit, and LockBit loves France.
In 2022, LockBit was used in 31% of known attacks globally, 3.5 times more than its nearest competitor, ALPHV. (You can read much more about why LockBit is the number one threat to your business in our 2023 State of Malware report.) As you’d expect, given its global preeminence, LockBit was also the most widely used ransomware in France, Germany, and the UK in the last twelve months.
However, LockBit dominates in France in a way that it doesn’t in its European neighbours. Between April 2022 and March 2023, LockBit accounted for an absolutely enormous 57% of known attacks in France. Over the same period, it accounted for 20% of known attacks in the UK and about 30% in Germany.
LockBit recorded 62 known attacks in France in the last twelve months, but no other gang registered more than seven. In the same period LockBIt was responsible for 33 known attacks in the UK while six other gangs also got into double digits.

LockBit’s outsized contribution to France’s misery is most clearly seen by highlighting its contribution on a month-by-month basis. The number of monthly attacks in France has been highly volatile, showing far larger variation than the UK, despite its proximity and the similarity of their economies and populations. That volatility is almost entirely down to how many or how few LockBit attacks occurred each month. In the last twelve months only one other gang has registered three known attacks in a single month (Royal in March 2023), while LockBit has matched or exceeded that figure eight times, and exceeded ten attacks in a month twice.

The reasons for this aren’t clear, but it may simply be that as the 800lb gorilla in the ransomware ecosystem, LockBit is best placed to exploit opportunities outside of the Anglosphere. Like a lot of ransomware, LockBit is sold as a service and attacks are carried out by independent criminal gangs, referred to as “affiliates”, which pay the LockBit gang 20% of the ransoms they extract. The French economy is large enough to provide a fertile hunting ground for cybercriminals. It is possible that some of LockBit’s 100 or so affiliates have decided to specialise there.
Conclusions
In the last 12 months, France was a globally significant hunting ground for ransomware gangs, and the country with the fifth highest total of known attacks. Within France, the government sector was over represented, suffering a higher proportion of known attacks than the government sector in the USA, Germany, and the UK. Much like the education sector in the UK, the French government sector should be alarmed that with an entire world of targets to choose from, it has attracted a disproportionate amount of attention.
France attracted enormous attention from gangs using LockBit, the most dangerous ransomware in the world. There were almost twice as many known LockBit attacks in France than in either Germany or the UK. In all, LockBit was used in 57% of known attacks in France, while the next most used ransomware, Vice Society, accounted for just 6%.
France does not so much have a ransomware problem as a LockBit problem.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; disable or harden remote access like RDP and VPNs; use endpoint security software that can detect exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like Malwarebytes EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Malwarebytes removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.